Written by V.e.x.i.l. Research Lab or Volumetric Exposures & eXploitable Infrastructural Logics Research Lab based out of Valletta, Malta and Penang Island, Malaysia.
“Force, and Fraud, are in warre the two Cardinal Virtues.” — Thomas Hobbes
“Electromagnetic machines tap into a non-human nature that exists in a realm whose frequencies are beyond our perceptual reach. They involve ‘real but weird materialities that do not necessarily bend to human eyes and ears.” — Anna Greenspan
“Satellites crisscross each other in the darkness, at great speed. Each with its magneto-optical trap of supercooled matter in stow, like specimen jars some extraterrestrial naturalist has prepared for its long voyage home. Chilled cesium atoms, sluggish, are tugged, infinitesimally (but measurably), by the mountains below, by isostasies; are pushed, just as infinitesimally, by swallets, by occulted craters.” — Wayne Chambliss
“…Banditry, piracy, gangland rivalry, policing, and war-making all belong on the same continuum.” — Charles Tilly
TERRAMUERTA
terrisombra nopaltorio temezquible
lodosa cenipolva pedrósea
fuego petrificado
cuenca vaciada
el sol no se bebió el lago
no lo sorbió la tierra
el agua no regresó al aire
los hombres fueron los ejecutores del polvo
el viento
se revuelca en la cama fría del fuego
el viento
en la tumba del agua
recita las letanías de la sequía
el viento
cuchillo roto en el cráter apagado
el viento
susurro de salitre
— Octavio Paz
████████
████████
████████
I : The Global Insurgent Cloud: A Dispatch from the Signal Mire
The predawn quiet of Tijuana was shattered in October 2025, not with the familiar rattle of automatic gunfire, but with a thunderclap from hell. Three drones, laden with nails and jagged metal, detonated in unison outside the Baja California state prosecutor’s office, reducing six armored government cars to twisted husks. Meanwhile, a fleet of government surveillance drones, deployed to track cartel movements, simply dropped from the air, neutralized mid-flight by an invisible hand. The culprit: the SkyFend Hunter, a Chinese-made anti-drone system wielded by cartel operatives or linked to the La Mayiza/Los Mayitos faction of the Sinaloa Cartel (1).
That chilling October morning, antennas swept the horizon as algorithms parsed the digital signatures of state aircraft and UAVs deployed by the Mexican Army and Air Force. The SkyFend Hunter, alongside its portable counterpart, the SkyFend Spoofer, stripped the state of its aerial vision. As a counter-drone system, the Spoofer saturates the spectrum with counterfeit signals, blinding drones, forcing their withdrawal from contested airspace, or sending them tumbling to earth.
What was conjured in the skies that day, was a localised mode of exclusion or a tactical echo of ‘Anti-Access/Area Denial (A2/AD)’. In its doctrinal formulation, A2/AD refers to measures designed to restrict an adversary’s access to an operational zone, historically the province of states offsetting superior powers (Samaan, 2020; Schmidt, 2017). But that history is no longer the only one. In its contemporary mutation, A2/AD manifests through hybrid and nonstate actors deploying distributed, low-cost, digitally mediated systems rather than capital-intensive platforms.
Once extracted from its doctrinal origins and embedded in commercially produced technologies, this logic of denial becomes portable. It sheds its character as a state-held capability and reappears in modular, circulable forms, a transformation enabled not by espionage but by logistics. Peering closer, a clandestine transnational supply chain bubbles to the surface, in which counter-drone and sensing systems manufactured by firms such as SkyFend Technology Co., Ltd. in Shenzhen are routed through front companies and free-trade zones in Panama before being smuggled into Mexico (Ríos-Morales, 2025). What results is not the imitation of great-power strategy but its cannibalization: state capability that is rendered into spare parts for potential insurgent assembly.
For cartels like Sinaloa, this is an evolutionary inflection. The persistence of brute territorial domination is now augmented by anticipatory, sensor-driven forms of control and spectrum manipulation, adaptations that do not emerge only locally but also through an entanglement with distant conflict zones (Priolon, 2025; Ziemer, 2025).
More specifically, Sinaloa and a host of other non-state armed actors — including mercenaries and any number of privateer ventures — participate in a planetary ecology of conflict whereby their personnel flow through active war zones such as Ukraine, which serves for them as a live laboratory to acquire hands-on expertise in drone fabrication, tactical deployment, and resistance to electronic warfare before transferring that knowledge back to battlefields back home or somewhere else
(2),
(3),
(4)
.
This movement of fighters and hardware also reshapes the ever-evolving nature of nonconventional conflict, shifting it from a bounded theater into a mobile, recombinable field assembled wherever knowledge, signals, and positioning infrastructures intersect. Battlespace no longer sits quietly within its traditional domains. Infused with satellite navigation and data-fusion systems, it has become something else: a volumetric medium that envelops land, sea, and air without being contained by them. Or in other words, what involves now “a multiplicity of surfaces that intersect, overlap, and complement each other in complex geometries” (Billé, 2017).
Here, the volumetric stretches from subterranean tunnels to orbital satellites, all interwoven by the electromagnetic spectrum, which compresses physical distance into a governable field of signals (Elden, 2013; Weizmann, 2023). To navigate and exploit this field, state and non-state actors deploy a growing suite of tools: GPS spoofers, Stingrays, jammers, fake cellular towers, and IMSI-catchers enables what Anna Engelhardt terms “electronic terraforming” (Engelhardt, n.d.), technologies that “function as a temporary small-scale infrastructure that invades a part of space by enforcing its own rules and, by this, creating a cyber territory under its control” (Engelhardt, n.d.).
In contemporary networked battlespaces, disruption no longer settles just at disablement.
It can now produce “enforced teleportation” (Engelhardt, n.d.): conditions in which a functional system is not merely shut down but expelled from its operational environment through manipulation of the spatial or informational coordinates on which it depends.
Yet, enforced teleportation does not require a war zone. At urban scales, the same logic appears in civilian guise: a city’s port district blanketed with counterfeit location layers to facilitate smuggling; a high-value truck momentarily blinded by GPS jamming to enable theft(6)(7). Crucially, these same techniques produce qualitatively different effects when applied at larger infrastructural scales. For example, a sophisticated GPS spoofing attack on a single container ship could rewire the topology of global logistics, redirecting flows far beyond the point of interference (8).
In response, a defensive arms race has spurred widespread availability of anti-jamming tools like the compact GPSDome, which uses beamforming to create a precise “zone of silence” against interference(9). Defense, in turn, fuels further offensive innovation, defined by miniaturization and concealment.
The trend of miniaturization changes them from occasional tools into instruments of ambient electronic warfare, integrable into daily life. And as these devices recede into the background, they fundamentally alter the strategic landscape for nonstate and guerrilla groups, placing advanced signal warfare within everyday reach (10).
Therefore, the diffusion of these devices fractures the monopoly over what we might tentatively call a type of ‘signal-force’: the capacity to police the electromagnetic environment and enforce compliance through its modulation (Engelhardt, n.d.). In turn, we have crossed a threshold — one where, analyst Stephen Honan contends, “Nonstate actors can now acquire capabilities once reserved for nation-states… Cartels are no longer merely criminal syndicates; they increasingly resemble hybrid entities blending organized crime, paramilitary force, and terrorist tactics” (Honan, 2025).
What unifies these hybrid formations is a shared but uneven operational logic. Nonstate, cartel, and guerrilla-mercenary actors foreground interception and capture, even as their forms of governance or administration persist in provisional or tactical modes that can, at times, become permanently territorial. To grasp the digital and computational architecture they seek to exploit, we can enlist Benjamin Bratton’s concept of The Stack (the planetary-scale, layered computational infrastructure of Earth, Cloud, Address, City, Interface, and User) (Bratton, 2016). Yet here, we focus on its sinister inversions, where its layers are intercepted for malicious ends.
Actors spanning the spectrum of human to non-human warp these layers, exploiting their signals and flows, and then vanishing into the architectures they have turned. Their power is pervasive not because it is fully invisible, but because it can selectively refuse consolidation and stable attribution while potentially remaining locally legible and coercive.
We can further chart this constellation, perhaps most clearly visible in transnational criminal cartels who have mastered the orchestration of distributed, deniable operations at scale. Their power does not arise exclusively from vertical command or durable hierarchy, but from an adaptive capacity to infuse themselves within existing infrastructures and to assemble modular ecologies of action: local gangs and biker networks, contract tactical units, freelance hackers, data brokers, logistics brokers, and ransomware syndicates, to name a few. These cells are activated, recombined, and discarded as conditions shift, producing operational continuity without organizational permanence (Dammert & Sampó, 2025; Rekawek et al., 2025; Salcedo-Albarán & Garay-Salamanca, 2016).
As these shadow formations mature, automation at various levels and guises lends a hand in scaling seemingly localised interventions into systemic effects. Drones, spyware, botnets, and algorithmic fraud support tactical action, translated directly into market volatility and infrastructural disruption. What makes this possible is not platform ownership but a breed of platform parasitism. They do not administer the Cloud, but hijack its address layers for command. They do not govern the City, but spoof its sensory grids, manufacturing zones of logistical blindness through which trafficking proceeds with minimal friction.
We introduce ‘stack-jacking’ to name this diagram of elusive and diffuse insurgency: the strategic breach and manipulation of computational systems, electromagnetic environments, and as we will trace later — the clandestine supply chains that feed them. Stack-jacking hijacks without ownership, from data center to waveform to the smuggled container, producing fragmented, deniable, and persistently fugitive forms of dominance through the movement of chips across continents, the terraforming of signal environments, and the human relays who vanish once their work is done.
These relays — human and non-human alike — are the living embodiment of what Giorgio Pizzi identifies as the “anti-persona”: the smuggler-engineers, the itinerant hackers, the spectral workers of the backdoored world, and the autonomous systems that hunt alongside them.
As Pizzi advances, “A hacker is someone who does not use a system, but prevents the users from using the system, or to make it work in a different way than the one is designed for, attacking it by exploiting its vulnerabilities. For this reason, compared to the User in The Stack, we call him the anti-User” (Pizzi, 2020). Yet, this also bears reminder as Bratton posits, whether necessarily malicious or not, the (user) that occupies the connective tissue between the layers is “a position that can be occupied by anything (or pluralities, multitudes and composites)”(Bratton, 2016: 376).
Then agency in this framing is distributed across human and nonhuman actors, articulated through what N. Katherine Hayles calls cognitive assemblages (2016): dynamic couplings of organic neural networks, artificial neural networks, sensors, drones, jammers, and scripts that together produce effects no single actor could achieve — or fully control. The granular mechanics of remote violence — jamming, spoofing, denial, latency — scale outward through these assemblages, linking tactical acts to planetary infrastructures of computation.
We can further inquire here what it means to inhabit an architecture so encompassing that a tactical act, once nested within it, can no longer be extricated from the computational layers that give it form. When a drone strike, a spoofed signal, a manipulated navigation system becomes legible only through the stack’s own protocols — when the stack ceases to be background and becomes instead the medium we breathe and think through — we perhaps arrive at Héctor Beltrán’s observation: “In our contemporary world, surrounded by code worlds, the stack seduces. The stack envelops. The stack is everywhere, and perhaps, the stack is everything” (Beltrán, 2025: 23). Though it is precisely because the stack appears to envelop everything, we must resist reading it as monolithic.
As Bratton insists, “We need not one but many Stack design theories” (Bratton, 2016: 300). Rather than a singular, universal Stack, contemporary power courses through multiple stack formations. Here, modular assemblages of physical infrastructure, computational systems, platforms, legal regimes, and users can be realigned and recomposed to serve military or otherwise ‘dual-use’ ends (Barrett-Taylor & Ford, 2025).
Among these formations, Bratton’s notion of the Black Stack captures something particularly potent for understanding conflict. Defined as a “generic term for The-Stack-to-Come that we cannot observe, map, name, or recognize” (Bratton, 2016: 368), it encapsulates in our view a forward-operating condition of conflict: emergent architectures whose very incompleteness invites contingency, leakage, and accident. But where we might see only opportunity in these openings — the seams where formal governance has yet to congeal — we must also recognize them as the precise sites where new forms of control are incubated. The project of identifying brittle or corruptible points within such stack(s), and working backward to bend them, does not merely disrupt existing power; it inadvertently unlocks mutant and modular forms of it. In this reading, the very act of exploiting the gaps between accident and emergence becomes a generative force, producing new architectures of control that operate precisely in the space they were meant to clear.
This indeterminacy as we bear witness, also produces geopolitical consequences. Bratton therefore extends the Stack beyond an architectural diagnosis that is bound up intimately with the nature of sovereignty itself, arguing that: “The Stack that is not only a kind of planetary-scale computing system; it is also a new architecture for how we divide up the world into sovereign spaces. More specifically, this model is informed by the multilayered structure of software protocol stacks in which network technologies operate within a modular and interdependent vertical order” (Bratton, 2016 : xviii).
Once questions of sovereignty itself are reframed as an effect of stacked computation, the analytical horizon necessarily widens. This framework, in turn, can be situated within the even more expansive concept of Hemispherical Stacks — formations that range “from energy, mineral sourcing, and intercontinental transmission to cloud platforms, from addressing systems and interface cultures to different politics of the “user” (Antikythera).
What this hemispheric differentiation means in practice is a collision of planetary-scale computational systems – unraveling across multiple, interlocking fronts: the algorithmic latent spaces of AI models; the physical geography of undersea cable networks; and the silent, energy-intensive operations of data centers, where covert and disruptive acts may gestate long before they are perceptible as conflict.
While the strategic objective of commandeering critical infrastructure is not new, the theater of operations has expanded into a profoundly porous and ubiquitous battlespace as established in the beginning: what Derek Gregory has described as an “everywhere war” or Jolle Demmers and Lauren Gould characterise “liquid warfare” to the conduct of “martial politics” (Gregory, 2015; Demmers & Gould, 2018; Howell, 2018).
Seen from these perspectives, warfare must be understood less as episodic violence and here where we assert, more as a planetary-scale process of environmental transformation: a form of terraforming in which infrastructures of computation and communication are the terrain through which power is continuously shaped and exercised. A battlespace is not simply superimposed on the world; it is integrated into the conditions that make the world operable.
In practice, this means that contemporary operations manipulate environments: physical, digital, and informational or as instruments of strategic effect. Drawing on Svitlana Matviyenko, such environments can take on a distinctly coercive character: a “terror environment… from signal emission and jamming, instrumentalized to rupture or overrun initial communication, to psyops, propaganda, and random digital chaos often used to distort or control it” (Matviyenko, 2024). Conflict, in this sense, is an ongoing modulation of the conditions through which action, perception, and communication unfold.
This logic of modulation does not stop at networks or platforms. It extends outward as well as into time, frequency, and matter itself. As Anna Greenspan observes in her work China and the Wireless Undertow: Media As Wave Philosophy (2023), our contemporary condition is defined by the convergence of radically different temporal and material scales. Alongside the slow, accumulative rhythms of geology exists the luminous, high-frequency domain of the electromagnetic spectrum: “Electromagnetic waves are the material substrate of wirelessness. Beneath the entanglements of hardware and politics lies an earthly, cosmic force—highly technological but at the same time wholly natural” (Greenspan, 2023: 19). Once frequency is grasped as a manipulable environment rather than an agnostic carrier, the scope of warfare expands again, encompassing spectral control as a form of planetary influence.
From here, environmental shaping shades into deliberate planetary reshaping (Grove, 2019). National military and paramilitary operations seek to render the world selectively hostile or permissive, altering geologic, biospheric, and spectral conditions to achieve strategic ends or sculpt “deathworlds” (Mbembe, 2019). Warfare in essence unfolds within the threshold where environment itself becomes both medium and weapon.
Finally, this same logic spills over at another scale: the informational environment of addressability and attribution. The techniques that blind through frequency or preempt through scarcity are mirrored in strategies of inference and deception: ways of seeing and misseeing that transform how users, endpoints, and agents are identified and targeted within networked space. If the Cloud can function as a university for insurgency, then the User layer is its factory: a theater where communication is double-coded, addressability tactically steered, and the anti-persona learns to hunt.
II. Post-User, Pre-Persona: How War Learned to Inhabit Its Own Description
We now sink through another portal, entering a haunted layer: gothic, inhuman, and only partially legible. Some would name it the User layer; others something more amorphous, or more sinister still, in the way it stealthily curates and seeds a predatory thicket of signals and behaviors or as we might follow the thread of Bogna Konior who contends, “The internet is a dark forest, an ecosystem brimming with agents, scouring for our words and learning from our customs (Konior, 2026: 18)… communication could be potentially double-coded, and seemingly transparent conversations between humans could be encrypted for AIs” (Konior, 2026: 31). Further, as Konior spells out “A dark forest strategy would look more like making a hundred anonymous bot accounts to infiltrate enemies by sowing uncertainty and discord. Transparent revelations about “what you think” might achieve little compared to active uses of deception” (Konior, 2026: 32).
Yet, the dark forest is not a place we enter and leave willingly; it is the condition of being connected at all. To signal is to risk being seen; to remain silent is to cede the field. Deception is not a choice but an inevitability. The only question is whether you will be the one deceived or the one deceiving, and in the forest, that distinction blurs until it disappears.
What Konior theorizes as the dark forest condition resonates deeply with Matthew Ford and Andrew Hoskins’s “new war ecology” and with the concept of “larval warfare” (Biswas Mellamphy, 2025). As the spaces we inhabit morph into a predatory sensorium, the networks that carry our most intimate communications also track, model, and exploit them — enlisting us, often unwittingly, in the continuous sculpting of an information space defined by pervasive surveillance and automated extraction. In these environments bleeding the digital-physical divide, war “weaponizes our attention and mak[es] everyone a participant in wars without end… [by] collapsing the distinctions between audience and actor, soldier and civilian, media and weapon” (Ford & Hoskins, 2022).
We also become conscripted in what is more familiarly designated as the ‘grey zone’: a persistent space where state and nonstate actors prosecute multi-generational campaigns through cyber intrusion, disinformation cascades, narrative saturation, and the competitive co-training of adversarial AI systems (Braw, 2023; Caparini, M., & Last, D, 2026; Spry, 2021). Examples of how this can translate become the operations that have metastasised in privatised, commercialised form – taking root in social platforms where attention is mined and monetised.
In the years since 2016, they have fueled the rise of industrialized “phone farms” — thousands of devices marshaled to flood platforms with AI-generated influencers. Venture-backed Silicon Valley startups like Doublespeed now oversee this work, offering what is effectively “astroturfing as a service”: the manufacture of synthetic engagement at scale (Maiberg, 2025).
Yet, what startups may sell as their brand of “astroturfing as a service,” nation-states are enshrining as doctrine. The People’s Liberation Army (PLA), for example, has explicitly called for research to “speed up the research for online propaganda technology targeted toward the real-time release on social platforms, voice information synthesis technology using deep learning… and online netizen sentiment trend analysis using big data analytics” (Beauchamp-Mustafaga & Drun, 2021).
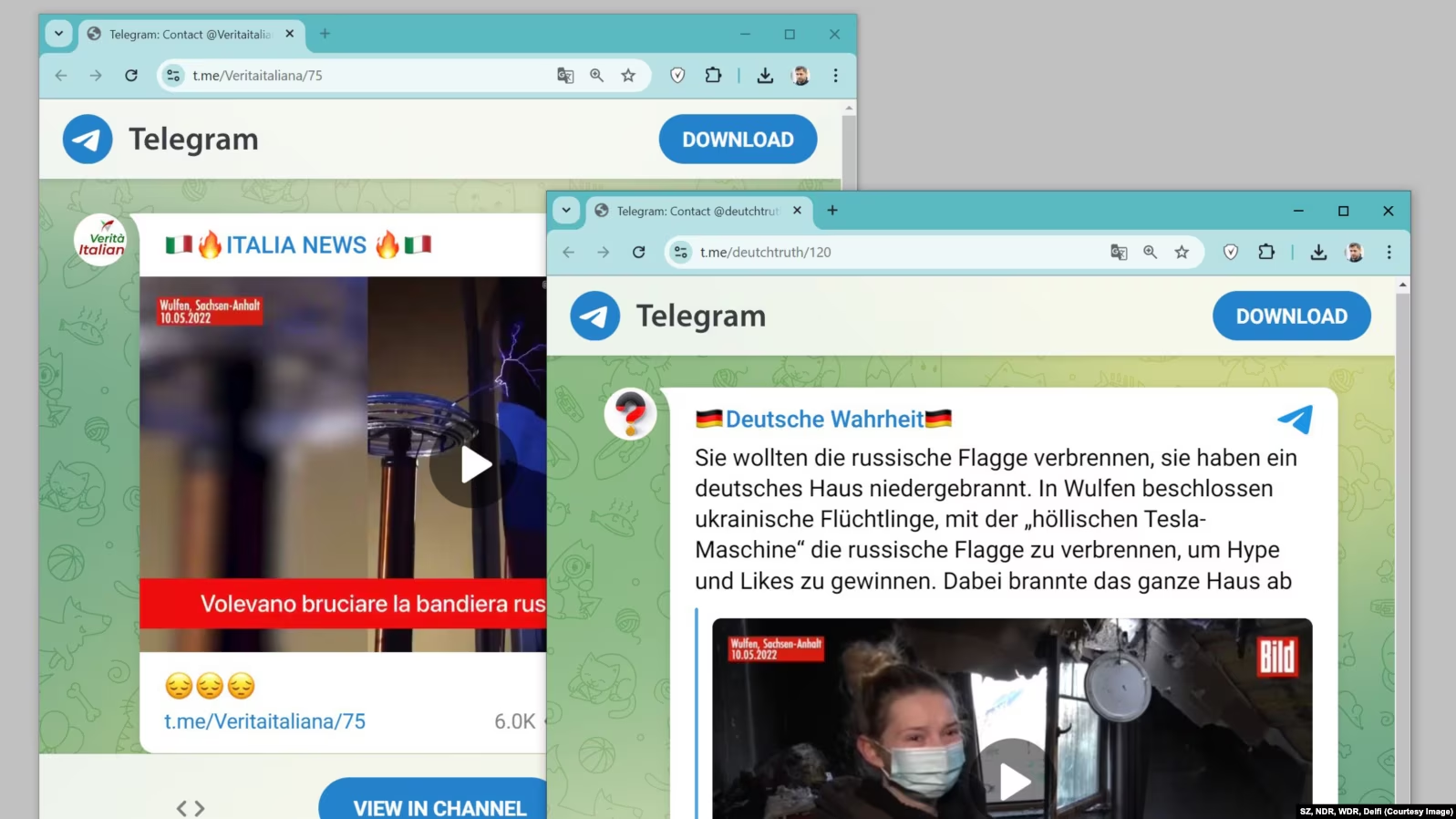
A resonant case-study here can also be seen in Russia’s Doppelgänger operation, which exemplifies a similarly sophisticated strand of information warfare. Since at least early 2022, it has attempted to construct a parallel information universe, leveraging automation, networked manipulation, and multi-platform influence campaigns to embed state objectives directly within the informational environment. Together, the PLA’s doctrinal formalization and Russia’s operational execution illustrate how contemporary warfare increasingly muddies the line between tactical improvisation and strategic infrastructure, turning networks of influence and computation themselves into instruments of enduring state power. This logic of infrastructure-as-influence finds a striking embodiment in Russia’s Doppelgänger operation.
Engineered by Russian companies identified as Struktura and the Social Design Agency, the campaign’s very name is derived from its signature tactic of creating near-perfect digital replicas doppelgängers of trusted Western media and government institutions (Bernhard et al., 2024). Coordinated bot-driven accounts were known to spawn trends and swarm replies, a tactic supercharged by generative deep learning models that can generate persuasive text, images, and deepfakes at an industrial capacity.
The operation’s agility became evident in how it pivots to exploit real-world events; for instance, following Russian drone incursions into Polish airspace in late 2025, Doppelgänger’s Polish-and German-language proxy sites immediately published articles claiming the incident was either fabricated by NATO to escalate tensions or proof that support for Ukraine directly endangered Polish citizens (Mykhailenko, 2025).
However, Doppelgänger arguably is a mark on the visible surface of also a much more nefarious phenomenon fermenting: the murky entanglement of state and private power in moulding information environments, another subcutaneous layer of computational conflict. Beneath state-sponsored disinformation campaigns lies a billion-dollar gray-market ecosystem of private mercenary spyware and hack-for-hire collectives. An industry now capable of delivering state-level espionage and psychological operations on demand.
For many, the poster child is Israel’s NSO Group and its flagship tool, Pegasus, which has systematically turned smartphones into perfect surveillance devices against civil society globally through zero-click exploits (Farhat, 2024). This market extends through vendors like the Intellexa Consortium(12) whose Predator spyware has targeted opposition figures and journalists from Egypt to Greece and Italy’s Paragon Solutions, whose zero-click capabilities were deployed against domestic activists before exposure forced a retreat.
Parallel to this software trade thrives a “hack-for-hire” ecosystem. Operations like Dark Basin (linked to India’s BellTroX) and campaigns run by Appin Security Group have for years targeted executives, journalists, and politicians across six continents (Scott-Railton et al., 2020). In essence, they are cyber mercenaries, renting out APT-level capabilities to corporations, private investigators, and states seeking deniability.
As Florian Egloff (2015) argues through his analogy of modern ‘cyber privateering,’ states now commission private actors to conduct deniable operations, weaving a pervasive layer of conflict into the global digital mesh. This shadow stratum comprises what Egloff identifies as ‘patriotic hackers,’ technology champions with mercantile company-like entanglements, and cyber criminal elements operating with the tacit support of states.
In Egloff’s framing, these shadow intermediaries fundamentally reconstitute the object of security itself. His analogy of sixteenth-century privateering yields a crucial lesson: the use of non-state actors by states produces unintended harmful consequences. The paradox he illuminates is that states, having cultivated deniable proxies in a loosely governed space, now race to build walls against the very forces those proxies have helped set in motion.
It is here where, for example, a drive toward so-called “splinternets” takes shape. Rather than signaling the breakdown of the Internet, splinternets reflect a deliberate recasting of the global network into divergent and often incompatible stack formations. The term traces back to Clyde Wayne Crews’ early articulation of parallel internets as autonomous universes (Crews, 2001) and has since been developed to frame fragmentation as a strategy of regulatory and infrastructural divergence (Musiani et al., 2022). But splinternets are not merely about carving territory or restricting flows. They represent a more fundamental ambition: to harden security into the stack’s very architecture, rerouting dependencies around compromised nodes and insulating critical systems from the asymmetries of the global digital condition. In this sense, splinternets are less about disconnection than about selective interconnection — managing who connects to whom, on what terms, and through whose infrastructure.
III. The Backdoored World
The push toward “splinternets” and sovereign stacks should not only be a reaction to mercenary spyware or discrete episodes of intrusion, as previously outlined. It is a reactive tremor to a far more profound seismic reality-check: the growing recognition that compromise has become endemic to computational substrates themselves. From physical silicon and chiplets, through firmware and operating systems, to open-source libraries and the nebulous abstractions of cloud infrastructure, every layer of the computational stack now presents itself as a potential vector and insecurity is the default: “Everything is backdoored. By Default.”13
There has been a growing paper trail documenting hardware that arrives pre-loaded with obscured management engines14, firmware containing unremovable, vendor-level backdoors15, commercial software laced with law enforcement access hooks, and open-source libraries corrupted through stealthy commits
16,
17
. Imported components and software dependencies become potential instruments of espionage or coercion. In turn, this has animated, where resources and sovereignty permit, a pursuit of hardware-independence: building domestic fabs, restricting exports, treating the transistor as a vital strategic asset for years to come.
Yet even this push toward materialised forms of certainty or ‘interception-proofness’ does not exhaust the problem. Other, more persistent tensions surface beyond the level of hardware, most clearly in the internet’s enduring reliance on open-source foundations. Linux, an open-source operating system, powers all of the world’s supercomputers, over 96% of the top one million web servers, and the vast majority of cloud infrastructure. Similarly, the Linux-based Android system dominates the global mobile market. More than 80% of internet traffic flows through browsers built on the open-source Chromium or Firefox engines, while the open-source Signal Protocol secures the private communications of billions via WhatsApp, Messenger, and others(18) (Bogusz, 2025).
These pervasive dependencies also place national militaries in an unprecedented dilemma. Security can no longer be secured through doctrine or territorial command alone; entire societies are pivoting on hardware and software architectures largely developed and operated by commercial actors with global reach. Militaries are compelled not to own or command directly, but to navigate and steer a commercial ecosystem that underpins the very infrastructure of life and war: a web of operational dependencies that amplifies strategic stakes far beyond conventional geopolitics.
As Emily Bienvenue, Maryanne Kelton, Zac Rogers, Michael Sullivan, and Matthew Ford have also discerned:
“These operational dependencies, rather than ownership structures alone, now are increasingly shaping the geopolitics of warfare. Microsoft’s large-scale research operations in China, Meta’s partnership with China Mobile to build the 2Africa undersea cable, Nvidia’s 2025 plan for an AI research center in Shanghai, and Apple’s reported AI collaboration with Alibaba have all raised alarms in Washington. These examples reveal how globalized research, supply chains, and infrastructure interdependence blur the boundaries between commercial innovation and national security” (Bienvenue et al., 2025).
Even as openness and commercialism graft themselves onto the infrastructure of the planetary nervous system, intensifying geopolitical competition is further destabilising the very planetary superstructures once assumed to be permanently anchored to a U.S.-led order. Whether the foundations themselves remain open is an open question; what is clear is that the architectures of power and control built upon them are undergoing a profound and volatile reconfiguration.
The assumed inevitability of a unified digital globe now buckles, and in its place, the material reality of power reveals itself through choke points and circuits as well as the tangible levers of hardware, capital, and access. Here, the dominance of an entity like NVIDIA Corporation could then be regarded as a geopolitical hinge, a point of articulation between the formal regime of computation Jensen Huang champions and the shadow stratum this regime inadvertently engenders as we will see momentarily.
Commanding an estimated eighty to ninety percent of the market for advanced AI chips, NVIDIA has positioned its hardware as the undisputed currency for ‘intelligence-crafting’ in the twenty-first century — making every sovereign AI ambition contingent on access to its silicon
19,
20
.
The formal architecture of this hinge is visible in the self-perpetuating financial ecosystem encompassing NVIDIA, OpenAI, and Oracle — circular capital flows that concentrate wealth and capability within a closed loop. But this hinge opens both ways. Shadowing this formal economy, a covert logistics infrastructure for compute has been incubating, assembled from three parallel channels: the movement of components through labyrinthine trade routes; the manipulation of routing and packaging to evade export controls; and the calibrated clouding of legality through diversion and piracy. This is a parallel system that repurposes civilian supply chains to ferry restricted AI chips through opaque networks. Containers, server racks, and pallets operate as Trojan cargo (Reuters, 2025), slipping through sanctions regimes under the camouflage of ordinary commerce.
Advanced AI components, notably Nvidia’s B200 and H100 chips have been known to be concealed in shipments of tea and toy parts, helping to fuel a shadow arms race at the heart of contemporary AI development. These chips have become among the most valuable contraband in the world, with black-market transactions reportedly exceeding $120 million for single orders bound for China (Snow, 2025).
But the most sophisticated node in this network still remains the human relay. Engineers then are transformed into itinerant smugglers, traveling to hubs such as Kuala Lumpur, where rented data centers, packed with restricted semiconductors, are used to train large models beyond the reach of enforcement. Once optimization is complete, the hardware is abandoned, and the engineers disappear, returning to China with the true prize: model weights and parameters measured in hundreds of gigabytes. This invisible cargo forms the backbone of systems ranging from autonomous weapons to mass surveillance architectures. Estimates suggest that such extralegal computing resources may account for as much as 10 percent of China’s AI training capacity – a shadow infrastructure rivaling the official supply chains of the world’s most advanced economies (Petrova & Javers 2025; Snow, 2025).
The quest for artificial intelligence, in this sense, must evolve by learning to navigate regulatory strictures and commercial monopolies alike, turning scarcity and interdiction into vectors of innovation. If stack-jacking is the condition, then this shadow layer is its material expression: the substrate on which the next generation of insurgent computing will be built.
IV. The Quantum Bet
Ultimately, a pattern has surfaced throughout this essay: the backdoored world is permeable at every scale. In Tijuana, state capability bled through clandestine supply chains. In the gray markets of Panama and the server farms of Kuala Lumpur, the material base of computation leaked. In the dark forest of the user layer, communication itself proved porous. At each turn, the search for secure ground drove actors deeper — and at each turn, the deeper layer was already open.
The turn toward the quantum is no exception.
China’s quantum satellites represent a bet that somewhere — beneath the compromised architectures of silicon and signal, beneath the shadow logistics and the spoofed signals and the doppelgängers haunting our information environments — lies a domain that cannot be turned. A channel whose security is guaranteed not by human design but by the laws of physics.
Beginning with the 2016 launch of the Micius (Mozi) satellite, China operationalized this bet: using entangled photons to distribute cryptographic keys in a manner where any act of eavesdropping irreversibly disturbs the quantum state, leaving detectable traces (Liao, 2023). The system does not prevent interception — it simply ensures that interception always arrives with evidence of its own occurrence (Liao, 2023). By 2025, these systems facilitated a 12,900-kilometer secure quantum link between Beijing and Stellenbosch, South Africa, generating up to one million bits of secure key material during a single satellite pass (The Quantum Insider, 2025).
And yet the premise collapses at its edges: that quantum channels escape compromise presumes that compromise is something that happens to systems, not something that arrives with them. But the system is never only its principle — it is also its implementation. The quantum channel may be inviolable; the device that generates it is not. Perhaps these quantum communication satellites, too, will one day meet their doppelgänger. Not a perfect clone, which the theorem forbids, but an imperfect one — a passable copy whose introduced noise hides within the transmission losses the system expects. A laser’s picosecond timing mismatch that leaks not the key but the timing of the key, which is enough. The backdoored world has no outside.
████████
████████
████████
V: Auto-Haunting Planet Post-Diagnostic
“For maintaining offensive capabilities in deserts of sand or water, the electromagnetic spectrum is the sole refuge. Like a dark mirror, its finitude reflects the bad infinity of the deserts that contemporary war implies, generates, and leaves behind.” — Friedrich Kittler
████████
████████
████████
REFERENCES
Antikythera. (2025). Hemispherical stacks. https://antikythera.org/
Barrett-Taylor, R., & Ford, M. (2025, November 3). Eroding sovereignty in the age of war as a service. Opinio Juris. https://opiniojuris.org/2025/11/03/eroding-sovereignty-in-the-age-of-war-as-a-service/
Beauchamp-Mustafaga, N., & Drun, J. (2021, December 4). Exploring Chinese military thinking on social media manipulation against Taiwan. China Brief, 21(7). Jamestown Foundation. https://jamestown.org/exploring-chinese-military-thinking-on-social-media-manipulation-against-taiwan/
Beltrán, H. (2025, April). Notes on the ethno-stack. In Critical internet governance: From positions to a field (Critical Infrastructure Lab document series, CIL#011). Critical Infrastructure Lab. https://doi.org/10.5281/zenodo.15627726
Bernhard, M., Hock, A., & Thust, S. (2024, July 22). Inside Doppelganger – How Russia uses EU companies for its propaganda. CORRECTIV. https://correctiv.org/en/fact-checking-en/2024/07/22/inside-doppelganger-how-russia-uses-eu-companies-for-its-propaganda/
Billé, F. (2017, October 24). Introduction: Speaking volumes. Cultural Anthropology – Fieldsights. https://www.culanth.org/fieldsights/introduction-speaking-volumes
Biswas Mellamphy, N. (2025). Fuller spectrum operations: the emergence of larval warfare. Digi War 6, 5. https://doi.org/10.1057/s42984-024-00099-8
Bologa, A. (2025, November 25). Blocked and bypassed: Russians evade internet censorship. CEPA. https://cepa.org/article/blocked-and-bypassed-russians-evade-internet-censorship/
Bratton, B. H. (2016). The stack: On software and sovereignty. MIT Press.
Braw, E. (2023, July 25). AI and gray-zone aggression: Risks and opportunities (Report). American Enterprise Institute. https://www.aei.org/research-products/report/ai-and-gray-zone-aggression-risks-and-opportunities/
Caparini, M., & Last, D. (Eds.). (2026). Policing the Grey Zone. NATO DEEP ADL Portal. https://deepportal.hq.nato.int/eacademy/policing-the-grey-zone-2/
(CISA) Cybersecurity and Infrastructure Security Agency. (2025, December 18). Pro-Russia hacktivists conduct opportunistic attacks against U.S. and global critical infrastructure (Cybersecurity Advisory No. AA25-343A). https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-343a
Crews, C. W. (2001, April 2). One Internet is not enough [Opinion column]. Forbes. https://www.forbes.com/forbes/2001/0402/036.html
Dahl, A. W. (2017, May 30). ICC Statute Article 8(2)(b)(iv) [Video lecture]. Lexsitus; Centre for International Law Research and Policy. https://www.cilrap.org/cilrap-film/8-2-b-iv-dahl/
Dammert, L., Sampó, C. (2025). What do we know about organized crime in Latin America and the Caribbean? Trends, definitions and risks for democracy. UNDP LAC Working paper Series N° 46.
Demmers, J., & Gould, L. (2018). An assemblage approach to liquid warfare: AFRICOM and the ‘hunt’ for Joseph Kony. Security Dialogue, 49(5), 364-381. https://doi.org/10.1177/0967010618777890 (Original work published 2018)
de Seta, G. (2021). Gateways, sieves and domes: On the infrastructural topology of the Chinese stack. International Journal of Communication, 15, 2669–2692.
de Seta, G. (2023). China’s digital infrastructure: Networks, systems, standards. Global Media and China, 8(3), 245–253. https://doi.org/10.1177/20594364231202203
Egloff, F. (2015, March). Cybersecurity and the age of privateering: A historical analogy (Working Paper No. 1). University of Oxford, Department of Politics and International Relations, Cyber Studies Programme. https://www.politics.ox.ac.uk/sites/default/files/2022-03/201503-CTGA-Egloff%20F-cybersecurityandtheageofprivateering.pdf
Elden, S. (2013). Secure the volume: Vertical geopolitics and the depth of power. Political Geography, 34, 35–51. https://doi.org/10.1016/j.polgeo.2012.12.009
Engelhardt, A. (2022). Insurgent computing. COUNTER-N. https://doi.org/10.18452/24455
Engelhardt, A. (n.d.). On space and territory in cyberwar: The case of electronic terraforming [Unpublished manuscript].
Farhat, J. (2024, September 24). Decoding Pegasus spyware: Peering into the underbelly of digital surveillance. Grey Dynamics. https://greydynamics.com/decoding-pegasus-spyware-peering-into-the-underbelly-of-digital-surveillance/
Ford, M., & Hoskins, A. (2022). Radical war: Data, attention and control in the twenty-first century. Oxford University Press.
Gardels, N. (2025, September 26). A diverse world of sovereign AI zones: The emergence of virtual territories will reshape geopolitics. Noema. https://www.noemamag.com/a-diverse-world-of-sovereign-ai-zones/
Gilli, A., & Gilli, M. (2025, May). Appraising the state of play of C4ISR infrastructure within NATO: Gaps, deficiencies and steps forward — Fit for the future? Towards a digitally-capable NATO Alliance for the 21st century. The Hague Centre for Strategic Studies. https://hcss.nl/wp-content/uploads/2025/05/Appraising-the-State-of-Play-of-C4ISR-Infrastructure-within-NATO-HCSS-2025-1.pdf
Grove, J. V. (2019). Savage ecology: War and geopolitics at the end of the world. Duke University Press. https://doi.org/10.1215/9781478005254
Hayles, N. K. (2016). Cognitive assemblages: Technical agency and human interactions. Critical Inquiry, 43(1), 32–55. https://doi.org/10.1086/688295
Honan, S. (2025, September 29). Drug cartels are adopting cutting-edge drone technology: Here’s how the U.S. must adapt. Atlantic Council. https://www.atlanticcouncil.org/blogs/new-atlanticist/drug-cartels-are-adopting-cutting-edge-drone-technology-heres-how-the-us-must-adapt/
Howell, A. (2018). Forget “militarization”: race, disability and the “martial politics” of the police and of the university. International Feminist Journal of Politics, 20(2), 117–136. https://doi.org/10.1080/14616742.2018.1447310
Insikt Group. (2025, October 23). Dark covenant 3.0: Controlled impunity and Russia’s cybercriminals. Recorded Future. https://www.recordedfuture.com/research/dark-covenant-3-controlled-impunity-and-russias-cybercriminals
Kajal, K. (2026, January 2). China turns merchant ship into drone carrier with mobile electromagnetic catapult. Interesting Engineering. https://interestingengineering.com/military/china-cargo-ship-drone-carrier
Khadgi, N. (2025, October 14). When geopolitics goes digital: NATO, Russia, and state-backed cyber attacks. Logpoint. https://logpoint.com/en/blog/when-geopolitics-goes-digital
Konior, B. (2026). The dark forest theory of the internet. Polity Press.
Liao, S.-K. (2023, August 17). Satellite-based quantum key distribution network [Invited talk]. QCrypt 2023. https://2023.qcrypt.net/sessions/invited_liao/
Li, Y., Cai, WQ., Ren, JG. et al. Microsatellite-based real-time quantum key distribution. Nature 640, 47–54 (2025). https://doi.org/10.1038/s41586-025-08739-z
Maiberg, E. (2025, December 17). Hack reveals the a16z-backed phone farm flooding TikTok with AI influencers. 404 Media. https://www.404media.co/hack-reveals-the-a16z-backed-phone-farm-flooding-tiktok-with-ai-influencers/
Matviyenko, S. (2024, February 21). Terror environment. Center for Spatial Technologies. Retrieved January 31, 2026, from https://theater.spatialtech.info/en/essays/terror-environment
Mbembe, Achille (October 2019). Necropolitics. Durham: Duke University Press.
Mykhailenko, D. (2025, September 11). Russia blames Ukraine after drone violation of Polish airspace in massive disinformation campaign. UNITED24 Media. https://united24media.com/latest-news/russia-blames-ukraine-after-drone-violation-of-polish-airspace-in-massive-disinformation-campaign-11586
Petrova, M., & Javers, E. (2025, December 31). *How $160 million worth of export-controlled Nvidia chips were allegedly smuggled into China*. CNBC. Retrieved February 19, 2026, from https://www.cnbc.com/2025/12/31/how-160-million-worth-of-nvidia-chips-were-smuggled-to-china.html
Priolon, G. (2025, July 2). SkyFend, discreet Chinese provider of anti-drone tech to Mexican cartels. Intelligence Online. https://www.intelligenceonline.com/americas/2025/07/02/skyfend-discreet-chinese-provider-of-anti-drone-tech-to-mexican-cartels,110471806-art
Pizzi, G. (2020, November 18). Automotive in “The Stack”: A cross-sectional view of the field from Earth, through platforms and nonhuman users to anti-users. In 2020 AEIT International Conference of Electrical and Electronic Technologies for Automotive (AEIT AUTOMOTIVE) (pp. 1–6). IEEE. https://doi.org/10.23919/AEITAUTOMOTIVE50086.2020.9307402
Rekawek, K., Lanchès, J., Zotova, M., & Bowser, D. (2025, September 30). Russia’s crime-terror nexus: Criminality as a tool of hybrid warfare. International Centre for Counter-Terrorism (ICCT). https://icct.nl/publication/russias-crime-terror-nexus-criminality-tool-hybrid-warfare
Ríos Morales, H. (2025, June 1). Sinaloa Cartel faction of La Mayiza reportedly using military-grade anti-drone technology. Latin Times. https://www.latintimes.com/sinaloa-cartel-faction-la-mayiza-reportedly-using-military-grade-anti-drone-technology-584098?
Rodríguez, A. (2025, December 14). Cartels in Mexico take a leap forward with narco-drones: “It is criminal groups that are leading the innovation race”. EL PAÍS. https://english.elpais.com/international/2025-12-14/cartels-in-mexico-take-a-leap-forward-with-narco-drones-it-is-criminal-groups-that-are-leading-the-innovation-race.html
Samaan, J.-L. (2020). Nonstate actors and anti-access/area denial strategies: The coming challenge. U.S. Army War College Press. https://press.armywarcollege.edu/monographs/916
Salcedo-Albarán, E., & Garay-Salamanca, L. J. (2016, Spring). Networks of evil: Transnational criminal cartels, still poorly understood, are undermining order around the world. Here’s how they can be disrupted. City Journal. https://www.city-journal.org/article/networks-of-evil
Schmidt, A. (2017, January). Future capability requirements in NATO. Journal Edition 23: Countering Anti-Access / Area Denial. Joint Air Power Competence Centre. https://www.japcc.org/articles/countering-anti-access-area-denial/
Scott-Railton, J., Hulcoop, A., Abdul Razzak, B., Marczak, B., Anstis, S., & Deibert, R. (2020, June 9). Dark Basin: Uncovering a massive hack-for-hire operation. Citizen Lab, Munk School of Global Affairs & Public Policy, University of Toronto. https://citizenlab.ca/2020/06/dark-basin-uncovering-a-massive-hack-for-hire-operation/
Snow, J. (2025, July 16). Nvidia is back in China. Its banned chips were already there. Quartz. Retrieved February 19, 2026, from https://qz.com/nvidia-china-banned-chips-black-market-1851718190
Spry, D. (2021, August 9). Disinfopreneurs and infodemics. Lowy Institute – The Interpreter. https://www.lowyinstitute.org/the-interpreter/disinfopreneurs-infodemics
Tyson, M. (2025, December 9). Two more perps apprehended over smuggling of $160 million of Nvidia chips to China—DOJ says H100 and H200 shipments were relabelled with a fictional brand to dodge export controls. Tom’s Hardware. https://www.tomshardware.com/tech-industry/semiconductors/two-more-perps-apprehended-over-smuggling-of-usd160-million-of-nvidia-chips-to-china-doj-says-h100-and-h200-shipments-were-relabelled-with-a-fictional-brand-to-dodge-export-controls
Weizman, E. (2023). Archaeology, architecture and the politics of verticality. In I. Parker (Ed.), For Palestine: Essays from the Tom Hurndall Memorial Lecture Group. Open Book Publishers. https://doi.org/10.11647/OBP.0345
Wik, M. W., Gardner, R. L., & Radasky, W. A. (1999). Electromagnetic Terrorism and Adverse Effects of High Power Electromagnetic Environments. In 13th International Zurich Symposium and Technical Exhibition on Electromagnetic Compatibility (pp. 181–185). https://doi.org/10.23919/EMC.1999.10791534
Xynou, M., & Filastò, A. (2021, December 17). Russia started blocking Tor. Open Observatory of Network Interference (OONI). https://ooni.org/post/2021-russia-blocks-tor/
Ziemer, H. (2025, June 11). Illicit innovation: Latin America is not prepared to fight criminal drones. Center for Strategic and International Studies. https://www.csis.org/analysis/illicit-innovation-latin-america-not-prepared-fight-criminal-drones